Virtual servers, like physical machines, can be subject to hacker attacks. They look for weaknesses in the operating system, take advantage of the fact that users themselves ignore basic security rules. So how to build a system correctly and what tools should be used to protect a virtual server from attack, to take it out of the risk zone? Let’s consider the main points.
How hackers can break into a virtual server
Before considering how to protect your virtual storage from hacking, you need to understand how attackers can get into the machine and what it can lead to. The dangers that threaten VDS servers can be conditionally divided into 2 categories:
- Penetration. In this case, an attacker penetrates the system by brute-force or theft of account data. That is, he logs into the server as a registered user. The increased danger in itself is the entrance under the administrator account. This is how the hacker gains access to all information. He can copy, change it, make changes to the list of paid orders (in the event of a hacked online store), steal personal data of users, etc.
- Brute force. In this case, hacking of the virtual server happens by external action on the machine, which leads to its failure. A striking example of such an attack is DoS in all its forms. In this case, hackers send a huge number of requests to the virtual machine, which do not carry useful information. Their main task is to provide an increased parasitic load. As soon as it exceeds the norms set in the server settings, the computing resources deplete. The server hangs up, does not respond to requests. The work of all systems associated with it is paralyzed.
Therefore, it is necessary to protect each virtual server from any method of influence.
General recommendations
Virtual machine security is a complex of measures. And it is extremely unreasonable to rely on the fact that one of the measures can be taken to ensure absolute protection of the server from unauthorized access.
Among the general principles designed to maximize the security of VDS, we will single out:
- ensuring the protection of the server control channel;
- use of additional authentication means;
- the use of firewalls;
- SSL / TSL encryption;
- attraction of private subnets;
- use of monitoring tools;
- application of tools for automatic detection of third-party access;
- performing regular system audits.
Securing the server control channel
There is always a physical machine behind any virtual server. This applies to both private and shared cloud structures. It is in a separate, specially equipped room. The administrators who manage it are not sitting next to it. They use remote access. That is, they cannot control work locally. The easiest, most reliable, and proven way to ensure channel protection is to regularly update the software.
Each new version of the software fixes vulnerabilities identified by developers in previous generations. That is, it eliminates the tools that hackers could use. But remember: the updated software runs initially on the test server. Its compatibility with working programs is checked.
Using Additional Authentication Tools
Such a solution can increase the protection of the virtual server against hacking through penetration. It’s about two-factor authentication. Yes, too advanced hackers will be able to bypass it, but 90% of Internet attackers cannot overcome it. That is, they will not only need to crack the user’s password but also gain access to his phone to intercept the code or find additional keys. And this is a completely different level of hacking.
Using firewalls
A firewall is a special network filter that regulates the forwarding of all data packets that pass through it. You should use it for all devices connected to the Internet. The filter will automatically block incoming requests to connect to the virtual machine according to predefined settings. This is how the network administrator isolates the software from outsiders. Often, firewalls are already built into the operating system. They can also be configured, focusing on the tasks facing the server.
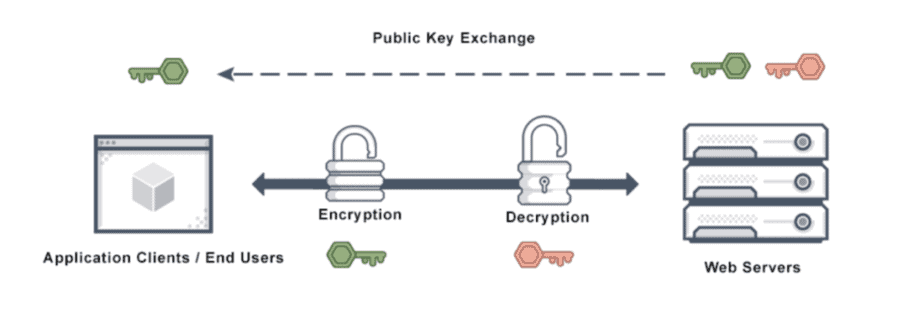
SSL/TSL encryption
Such a solution will ensure the protection of the communication channel of the user and the resource. It’s not just registered users. It is worth encrypting the data of all site visitors. After installing an SSL or TSL certificate, visitor information will be transmitted over encrypted channels using the HTTPs protocol. This will not protect the data from interception. However, the attacker will not be able to decrypt it and get the data they need. It is necessary to select the correct type and level of the certificate for a specific site.
Attracting private subnets
The attraction of private subnets will allow you to isolate part of the information system. This will increase the security of VDS hosting. It is optimal to isolate the server inside such a loop. As a result, at the public address, it will be invisible when directly navigating from the Internet. That is, only the virtual machines responsible for the user interface will be available to users. You can find the rest deep in the security settings. The advantage of private subnets for this task is that there is no direct connection to the Internet.
Using monitoring tools
It is relevant even for systems with 24/7 technical support. Not a single person, due to his physical capabilities, will be able to continuously monitor all operating parameters. The use of automated tools will significantly increase the likelihood of detecting changes in work. The administrator will only have to quickly respond to the message and take appropriate action. Modern monitoring tools allow you to monitor the work of the information system. They do this both from the inside and outside under different conditions.
Using tools to automatically detect third-party access
This solution is quite similar to monitoring. The only difference is in the specifics of the events. Such systems will react exclusively to unauthorized access, to repeated attempts to brute-force a password to different accounts. The accompanying events are analyzed in parallel. Instant response tools are also provided here. An example is the automatic change of the network filter settings.
Performing regular system audits
This is another kind of monitoring. Its actions help in obtaining information for subsequent analysis. The system will be able to register and check:
- The client’s actions.
- What information they have access to.
- The operations they perform with them.
- What applications they install.
Built-in analysis tools can handle huge amounts of versatile data.
Consider the peculiarities of the operating system
All of these recommendations can significantly improve the security of the virtual server. But you still need to consider which ones and how to use them for a particular operating system.
So, for virtual servers based on Windows, you should use:
- firewall, setting ports for user access with reliable IP;
- several accounts at the same time changing the administrator name. Create a separate account for each of them;
- restriction of rights for some accounts. You must perform those works that do not require administrator intervention from a separate profile;
- access with a password. Relevant for systems with public access. It will allow you to restrict the rights of persons who do not have administrative rights;
- automatic disconnection of sessions. After some time of inactivity, the user will have to re-enter the password for repeated access (relevant when several persons are working on the same computer);
- Microsoft Security Configuration Wizard (SCW) utility. Provided in the OS, capable of creating security files for all machines in the infrastructure.
Also, when working with Windows, you should provide access to remote desktops. Do this via the RDP protocol, use group, and local security policies.
In the case of servers running on Linux OS, you should perform VDS protection from hacking. You do this by:
- Activating the firewall.
- Porting and blocking ports.
- Using special utilities.
- SSH protocol.
- Security patches.
- Isolated startup systems.
- Working with passwords, etc.